Residential Proxy API: Bypass Antibots & CAPTCHAs
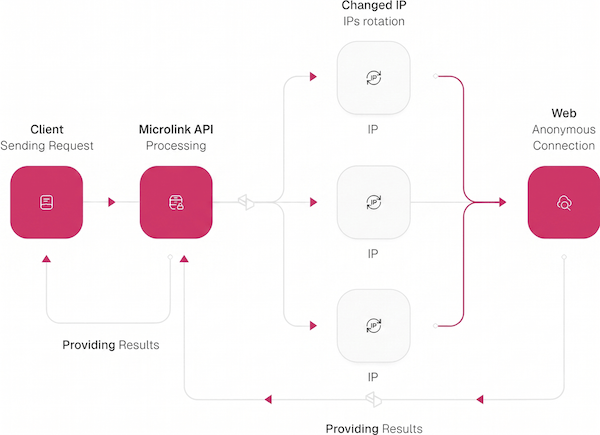
Zero-config web unblocker. The API auto-detects when a target is blocking, routes the call through a rotating residential pool, and picks the resolution path for that specific antibot or CAPTCHA provider — well-tested across the Top 500 most popular sites worldwide. Available on metadata, HTML, and markdown requests.
When the API detects that a target site is blocking a request, the call is automatically routed through a rotating residential proxy pool. The same pipeline absorbs antibot challenges and CAPTCHA gates, so metadata, HTML, and markdown responses keep arriving even when the target sits behind Cloudflare, DataDome, or Akamai. Today this runs on metadata, HTML scraping, and markdown — for screenshots and PDFs, see the FAQ below.
It is included on every Pro plan. No separate vendor, no per-challenge surcharge, no infrastructure to maintain on your end. The same behavior covers the Top 500 most popular sites worldwide.
Stop paying three vendors for one job
A residential proxy, an antibot detector, and a CAPTCHA solver are typically three separate vendor contracts, three SDKs in your package.json, and three lines on your monthly bill. Pro folds them into the same API key — fewer integration paths, fewer renewals to negotiate, lower stack complexity per request.
Default: automatic resolution
Send the request as you normally would. On any Pro metadata, HTML, or markdown request, the proxy layer engages automatically when the target requires it.
import mql from '@microlink/mql'
const { data } = await mql(
'https://www.bloomberg.com',
{ apiKey: process.env.MICROLINK_API_KEY }
)Already paying for a residential proxy?
If you have a dedicated provider or need a fixed country IP, pass the proxy URL on the proxy parameter. Microlink routes every sub-request — redirects, assets, dynamic fetches — through the same server.
import mql from '@microlink/mql'
const { data } = await mql('https://geolocation.microlink.io', {
proxy: 'https://myproxy:[email protected]:8001'
})How to confirm a request was proxied
Every proxied response carries an x-fetch-mode header ending in -proxy. That suffix is your proof the request went through the resolution layer — and that you are being billed under the Pro plan.
Stop renting three vendors for one job.
Pick the volume that matches your traffic. Automatic proxy resolution, antibot detection, and CAPTCHA handling are included on every Pro plan for metadata, HTML, and markdown requests.
Do I need to bring my own proxy?
proxy parameter. The bring-your-own proxy guide covers the URL format and credential handling.Does this work with screenshots and PDFs too?
proxy parameter (see the bring-your-own proxy guide), or write to us at Which antibot systems does Microlink bypass?
Does this bypass CAPTCHAs too?
How do I confirm a proxy was actually used?
x-fetch-mode response header. Any value ending in -proxy — for example fetch-proxy — means the request was routed through the proxy layer.x-pricing-plan header on the same response will read pro, confirming the request was billed against your Pro plan.